OWASP Security Assessment
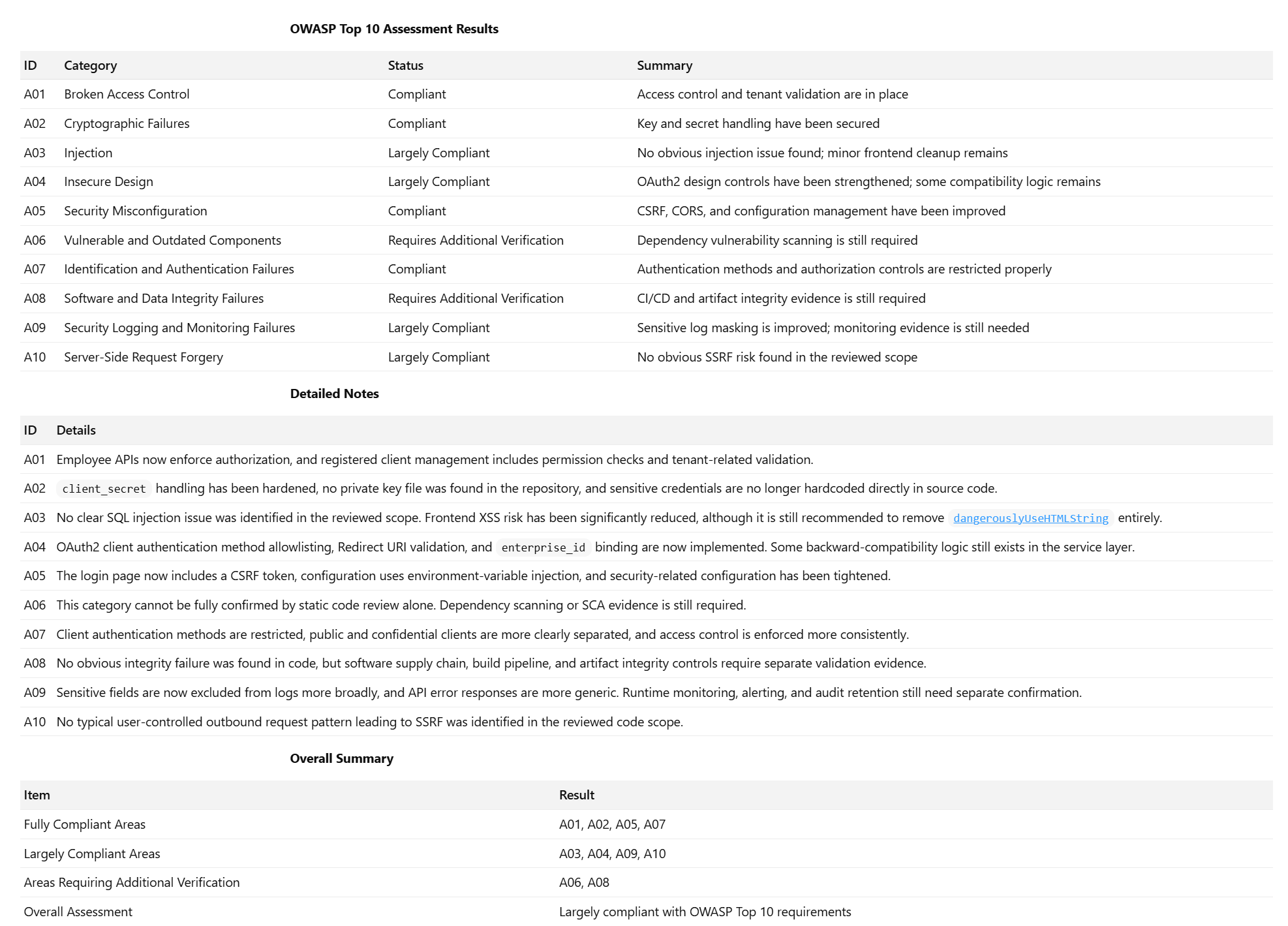
The diagram below presents the OWASP Top 10 security assessment results for the ShiftCareHR Tool, highlighting the system’s compliance status across key security risk categories.
How This Applies to ShiftCareHR
This assessment provides visibility into the security controls currently implemented within the system, as well as areas that may require further validation or improvement.
Most categories are either Compliant or Largely Compliant, indicating that core security measures such as access control, authentication, and configuration management are in place. However, certain areas—such as dependency management and data integrity validation—still require additional verification.
Developers and system administrators should use this report as a reference to:
- Understand existing security implementations
- Identify areas requiring further validation
- Ensure ongoing alignment with OWASP best practices
For API-specific security details, including authentication and authorization mechanisms, refer to the API Specification Document.
::: When building integrations or extending the HR Tool, ensure that your implementation aligns with the security controls and recommendations identified in this assessment.
All API requests must use bearer token authentication, as outlined in the API Specification Document. :::